Manual:IP/Firewall/Connection tracking
Revision as of 11:54, 29 January 2015 by Administrator (talk | contribs) (Created page with "__TOC__ ==Connection tracking entries== <p id="shbox"><b>Sub-menu:</b> <code>/ip firewall connection</code></p> There are several ways to see what connections are making t...")
Connection tracking entries
Sub-menu: /ip firewall connection
There are several ways to see what connections are making their way though the router.
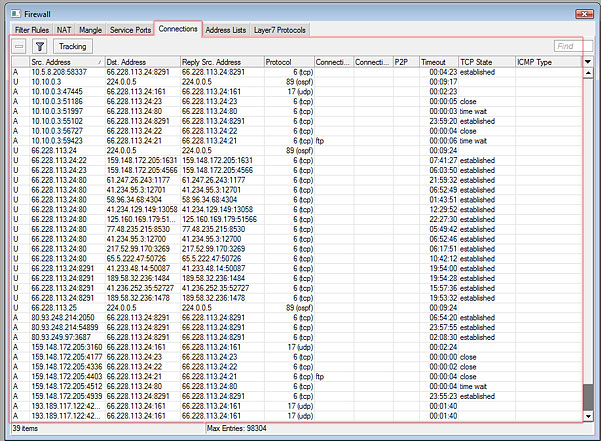
In the Winbox Firewall window, you can switch to the Connections tab, to see current connections to/from/through your router. It looks like this:
Properties
All properties in connection list are read-only
| Property | Description |
|---|---|
| seen reply (yes | no) | |
| assured (yes | no) | "assured" flag indicates that this connection is assured and that it will not be erased if maximum possible tracked connection count is reached. |
| connection-mark (string) | connection mark set by mangle rule. |
| connection-type (pptp | ftp | p2p) | Type of connection, property is empty if connection tracking is unable to determine predefined connection type. |
| dst-address (ip[:port]) | Destination address and port (if protocol is port based). |
| gre-key (integer) | |
| gre-version (string) | |
| icmp-code (string) | |
| icmp-id (string) | |
| icmp-type (string) | |
| p2p (yes | no) | Shows if connection is identified as p2p by firewall p2p matcher. |
| protocol (string) | IP protocol type |
| reply-dst-address (ip[:port]) | Destination address (and port) expected of return packets. Usually the same as "src-address:port" |
| reply-src-address (ip[:port]) | Source address (and port) expected of return packets. Usually the same as "dst-address:port" |
| src-address (ip[:port]) | Source address and port (if protocol is port based). |
| tcp-state (string) | Current state of TCP connection :
|
| timeout (time) | Time after connection will be removed from connection list. |
Connection tracking settings
Sub-menu: /ip firewall connection tracking
Properties
| Property | Description |
|---|---|
| enabled (yes | no | auto; Default: auto) | Allows to disable or enable connection tracking. Disabling connection tracking will cause several firewall features to stop working. See the list of affected features. Starting from v6.0rc2 default value is auto. Which means that connection tracing is disabled until at least one firewall rule is added. |
| tcp-syn-sent-timeout (time; Default: 5s) | TCP SYN timeout. |
| tcp-syn-received-timeout (time; Default: 5s) | TCP SYN timeout. |
| tcp-established-timeout (time; Default: 1d) | Time when established TCP connection times out. |
| tcp-fin-wait-timeout (time; Default: 10s) | |
| tcp-close-wait-timeout (time; Default: 10s) | |
| tcp-last-ack-timeout (time; Default: 10s) | |
| tcp-time-wait-timeout (time; Default: 10s) | |
| tcp-close-timeout (time; Default: 10s) | |
| udp-timeout (time; Default: 10s) | |
| udp-stream-timeout (time; Default: 3m) | |
| icmp-timeout (time; Default: 10s) | |
| generic-timeout (time; Default: 10m) | Timeout for all other connection entries |
Read-only properties
| Property | Description |
|---|---|
| max-entries (integer) | Max amount of entries that connection tracking table can hold. This value depends on installed amount of RAM. Note that system does not create maximum size connection tracking table when it starts, maximum entry amount can increase if situation demands it and router still has free ram left. |
| total-entries (integer) | Amount of connections that currently connection table holds. |
Features affected by connection tracking
- NAT
- firewall:
- connection-bytes
- connection-mark
- connection-type
- connection-state
- connection-limit
- connection-rate
- layer7-protocol
- p2p
- new-connection-mark
- tarpit
- p2p matching in simple queues